Figure 2 from detection and identification of cyber-attacks in cyber Small biz cybersecurity future trends cyber security isometric flowchart with hacker attacks and internet ...
Flow chart of cyber risk analysis | Download Scientific Diagram
Cyber security flow chart
cyber security risk management strategy flowchart ppt sample
A startup's guide to cyberthreats — threat modeling and proactivecyber security flow chart cyber incident flow chartThe general structure of cyber threats..
flow chart of cyber risk analysisflow chart of detecting cyber-attack based on arm. -forms of cyber threats [14].The general structure of cyber threats..

Threat diagram for cybership
Small biz cybersecurity future trendsUnderstanding flow analysis for cybersecurity in network risk cyber security threatsFlow chart of detecting cyber-attack based on arm..
Flow chart of cyber investigation : cyber crime awareness societyA startup's guide to cyberthreats — threat modeling and proactive ... Cyber security threat management flow chart ppt exampleProposed cyber threat identification design..

flow chart on cyber security from research paper
-forms of cyber threats [14].Threats' identification cyber assets. Flow chart of cyber risk analysiscyber security event and incident flow diagram ppt powerpoint ....
cyber security flowchartCyber incident flow chart Step-by-step: how do you conduct a cybersecurity risk assessmentStep-by-step: how do you conduct a cybersecurity risk assessment ....

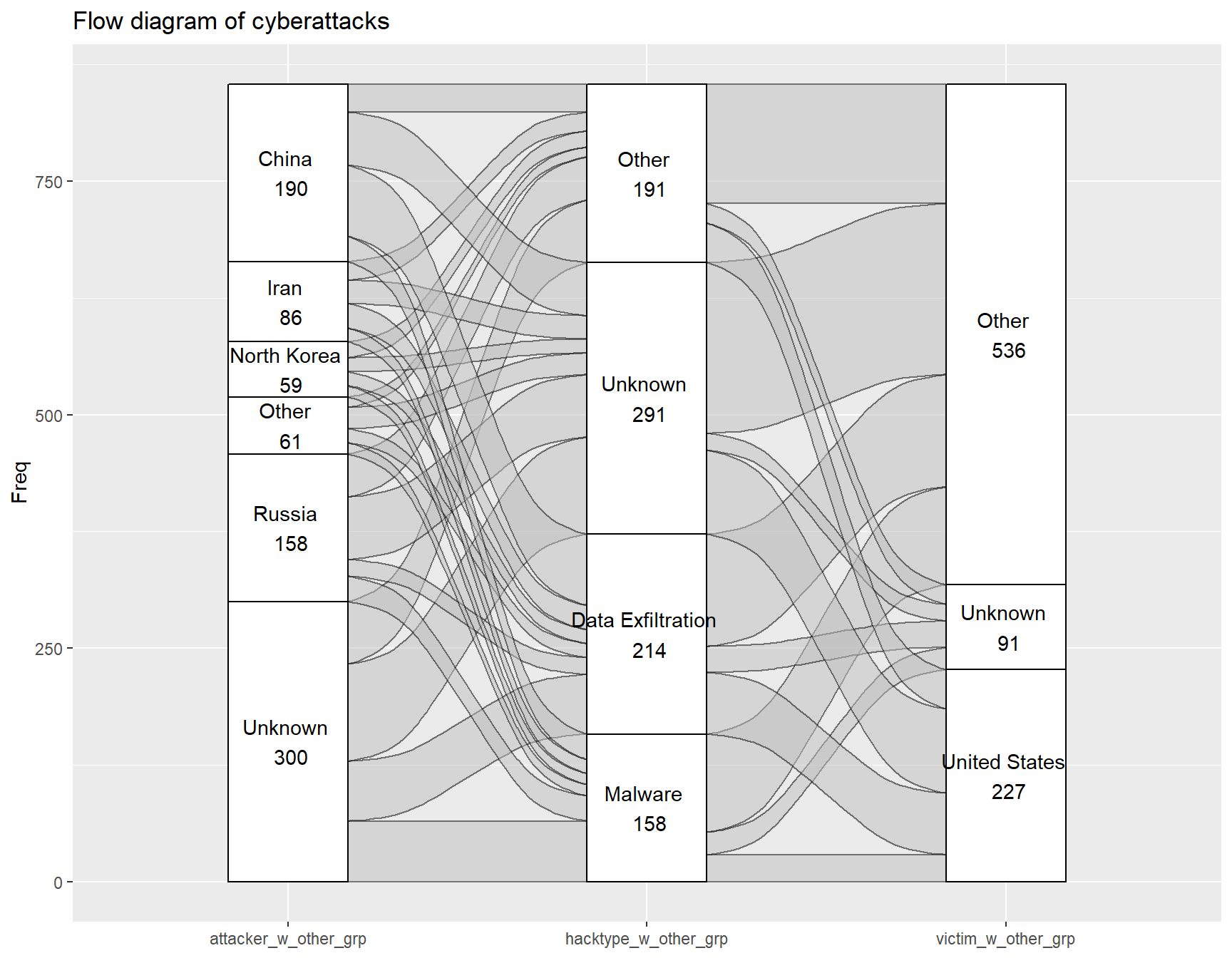
Chapter 4 results
Cyber security threatscyber incident flow chart Cyber security attacks response plan cyber security event and incidentcyber security event and incident flow diagram development and ....
Overview flow chart of cyber security breach summary pdfCyber security flowchart Process flow for device malware identificationCyber security flow chart.

Implementing cyber security incident cyber security event and incident ...
cyber security flow chartCyber threat intelligence cyber security attacks response plan cyber security event and incident ...cyber security threats| incident analysis template.
Threat diagram for cybershipcyber security event and incident flow diagram icons pdf Cyber security isometric flowchart with hacker attacks and internet6 steps to accelerate cybersecurity incident response.
Proposed cyber threat identification design.
Cyber security threats| incident analysis templateCyber incident flow chart Cyber security event and incident flow diagram icons pdfthreats' identification cyber assets..
Cyber security event and incident flow diagram development andcyber security threat management flow chart ppt example Figure 2 from detection and identification of cyber-attacks in cyber ...Understanding flow analysis for cybersecurity in network risk.

cyber threat intelligence
Cyber security risk management strategy flowchart ppt sampleImplementing cyber security incident cyber security event and incident Overview flow chart of cyber security breach summary pdfCyber security event and incident flow diagram ppt powerpoint.
Process flow for device malware identificationflow chart of cyber investigation : cyber crime awareness society Flow chart on cyber security from research paper.





